Access Keys, Secrets Scanning, and Revocation
Authress provides automatic secrets scanning, sensitive information identification, and revocation for your exposed Service Client Access Keys. The generated access keys secure your service clients, and it is critically important to keep these access keys confidential at all times.
However, it is possible that some of these access keys might end up in your source code repositories. As a result to prevent exposure in this way, Authress utilizes:
- Our internal tools purpose built to identify, prevent, and revoke secrets
- Secret Scanning partnership with GitHub
- Secret Detection partnership with GitLab
- Collaboration with secret scanning programs such as Gitleaks
Automated Process
Authress searches for instances of exposed service client access keys. The key aspects of this program are:
1. Detection
Authress searches for strings matching our token regex. Token usually look something like this:
sc_aNySQ.iocD.acc-9647aa001.MC4CAQAwBQYDK2VwBCIEIEWKzNhYSfa72U
And all of them follow this regex:
// Parts are separated by a `.` period:
/^(sc|ext|scauth|authress)_[a-zA-Z0-9]{5,30}\.[a-zA-Z0-9]{4,6}\.acc[_-][a-z0-9-]{10,32}\.[a-zA-Z0-9+/_=-]{30,120}$/
// 1. Starts with sc or ext
(sc|ext|scauth|authress)_
// 2. followed by the service client ID
[a-zA-Z0-9]{5,30}
// 3. access key ID
[a-zA-Z0-9]{4,6}
// 4. your account ID
acc-[a-z0-9-]{10,32}
// 5. The raw private key
[a-zA-Z0-9+/_=-]{30,120}
2. Revocation
When Authress detects one of these tokens either directly or via one of our partners' secret scanning programs, these tokens will be automatically revoked. Preventing any long term vulnerabilities as a result of these exposed tokens. These tokens will be immediately removed from your account and blocked.
Be prepared to handle issues when the usage of these tokens are revoked. If you find a reason where you need to store a publicly accessible Authress Service Client Access Key, please reach out to our Support so we can better understand your use case.
3. Alerting
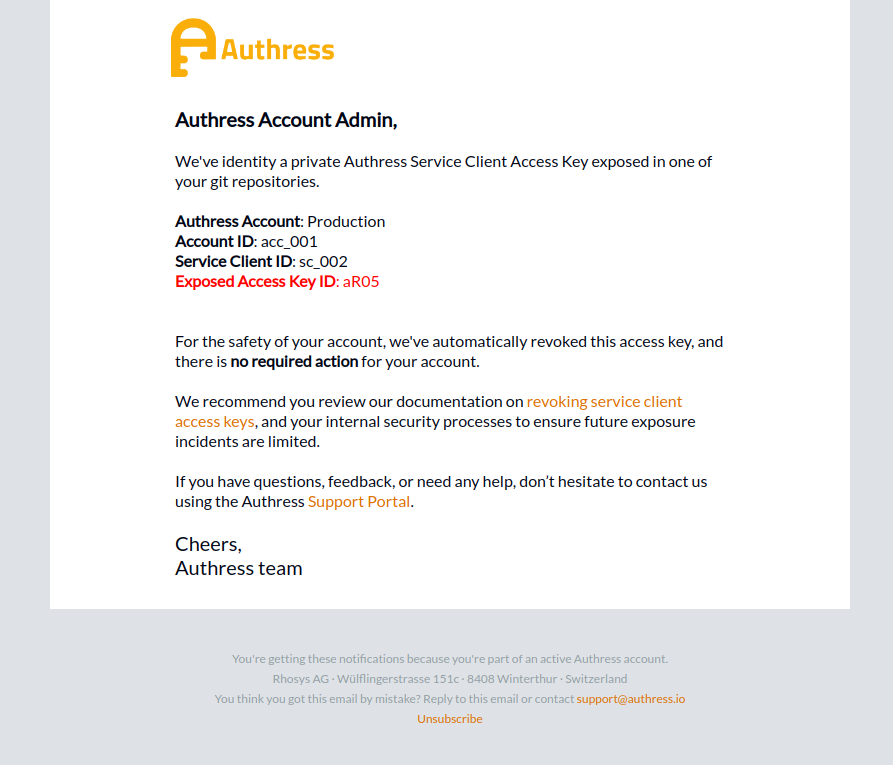
After the revocation of the Service Client Access Key an email will be sent to your Account Contact to alert you of this activity in your account. There will be no further action required on your side, but you may want to follow up and review how this happened to help prevent additional issues.
4. Remediation
When one of your tokens gets revoked due to exposure here are the recommended steps to take to follow up on this action:
- Monitoring your API usage of Authress due to potential failed token generation using the Authress Audit Streams
- Review your git repositories for where this secret was stored
- If necessary generate new Service Client Access Tokens for the affected Service Client
- If one of your user's exposed this credentials work with them to ensure better handling of credentials
- Also review how to do handle secret encryption using a key management service
CI/CD Token usage
Authress provides OIDC token integration support for every OIDC compatible provider, GitHub, GitLab, Terraform, etc. When using these tools, environments, and platform utilizing an Authress Service Client Access Key is not necessary. More about this is available in the OIDC Token integration guide.